NDR Queries by Karl Ackerman - Sophos
 Monday, July 3, 2023 at 10:17AM
Monday, July 3, 2023 at 10:17AM NDR Queries from Karl Ackerman on Vimeo.
Explanation of Power BI Licensing
 Friday, June 23, 2023 at 9:55AM
Friday, June 23, 2023 at 9:55AM I recently have had a need to learn more about Power BI licensing and I found this YouTube video that really explains it pretty well.
Using Dictation Function in Microsoft Office Desktop Apps
 Friday, June 16, 2023 at 11:18AM
Friday, June 16, 2023 at 11:18AM I have been finding myself using the dictation function, especially inside Word and OneNote, a lot more recently.
Dictation is a feature in Office 365 that allows you to use your voice to create content in Office apps. You can dictate text, punctuation, and even formatting commands. Dictation is available in Word, Excel, PowerPoint, OneNote, Outlook, and Publisher.
To use dictation, you need to have a microphone and a reliable internet connection. You also need to be signed into Office 365.
To start dictation, open an Office app and click on the "Dictate" button in the toolbar. The Dictate button is a microphone icon. Once you click on the Dictate button, your microphone will turn on and you can start speaking.
As you speak, the text will appear on the screen. You can use your voice to dictate text, punctuation, and even formatting commands. For example, you can say "period" to insert a period, or "bold" to bold the text.
You can also use dictation to create tables, lists, and other types of content. For example, you can say "table" to create a table, or "list" to create a list.
When you are finished dictating, click on the "Stop Dictation" button in the toolbar. The Stop Dictation button is a square with a red X in it.
Dictation is a great way to quickly create content in Office apps. It can be especially helpful if you are unable to type, or if you want to be able to create content while you are on the go.
Here are some tips for using dictation effectively:
- Speak clearly and slowly.
- Use natural pauses to indicate when you want to insert a new line or paragraph.
- Use the Dictate commands to insert punctuation and formatting.
- Review your work carefully after you have finished dictating.
Dictation is a powerful tool that can help you to be more productive in Office 365. By following these tips, you can learn to use dictation effectively and create content quickly and easily.
Here are some additional things to keep in mind when using dictation:
- Dictation works best in quiet environments.
- If you have a strong accent, you may need to speak more slowly or clearly.
- Dictation is not perfect, so you may need to edit your work after you have finished dictating.
Overall, dictation is a great way to save time and be more productive in Office 365. If you have a microphone and a reliable internet connection, I encourage you to try it out.
Workflow: Using OneNote as a Task Manager
 Thursday, June 15, 2023 at 2:12PM
Thursday, June 15, 2023 at 2:12PM One of the nice things about using OneNote as a task manager is the ease of being able to manipulate the information that you're putting into your task list. You can’t do that on paper!
I begin by selling up the section as a month/year heading. For example June 2023 would be my sectional heading. I then create separate pages for each day of the week labeling each page in the following way to make it easier for me to work with: 20230610 Saturday Task List.
I also create a floating page for Monthly Projects that I move with my current day page to keep the two together. I use the Monthly Projects for a reminder of ongoing things that I need to deal with that I can pull into a Day Task List as I work on them.
I keep a couple of other informational pages with the Monthly Project Sheet for quick referencing as well. It makes it easier for me to answer questions as they arise by keeping those listing easily accessible.
Since I create anywhere from 28 to 31 pages for the days in the month it is easier to create the first seven days and copy them as a group and adjust the information as needed once they are pasted back into the monthly section to create all the pages that I need. I also change the date on each page to match the date of the page. (Just the quirkiness in me)
This whole process only takes about 10 minutes to complete. A typical page layout is shown below.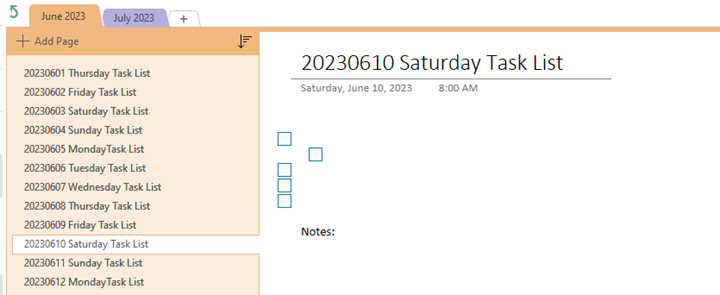
I typically work on my task list either the night before or in the morning when I start my day. It usually entails me bringing any unfinished tasks from the previous day over to be worked on. I add on any new tasks that may have come in via email or Teams communications. I also receive task functions from workflow notifications that I have created in our ticketing system to be included in the list. I then slide the task up and down list to place them in the order in which I want to attack the list. I will use tabbing to keep subtasks underneath a major heading to keep a project together (as you see in the example above). I use the check box function to mark off when the task is completed on the list.
What are the benefits of doing this in OneNote? There are several. First, because of the freeform nature of the application it can bend to my needs on a daily basis. Second, Search Notebooks allows a word search though all of your notebooks through one search bar. Third, Organization, being able to manipulate the data from day to day and within a day to reorder information and change it makes for a quick and easy control of the data that you are working with.
Let me know if this type of article is one that you would like to see more of.
Microsoft Teams 2.0 now in Public Preview
 Wednesday, May 31, 2023 at 12:22PM
Wednesday, May 31, 2023 at 12:22PM  Microsoft has released access to the Public Preview Program on March 27th, 2023. This feature has to be enabled in your O365 portal to become available. There are currently some things missing from the new version but later this year Microsoft will be turning this on as the default version. In listening to Microsoft’s Anupam Pattnaik, Product Lead for Teams he provided information on when it will be released and what to expect from the new Teams Platform.
Microsoft has released access to the Public Preview Program on March 27th, 2023. This feature has to be enabled in your O365 portal to become available. There are currently some things missing from the new version but later this year Microsoft will be turning this on as the default version. In listening to Microsoft’s Anupam Pattnaik, Product Lead for Teams he provided information on when it will be released and what to expect from the new Teams Platform.
Teams 2.0 is a ground up rebuild of the application. The goal was a 2x increase in speed while using less than half of the resources. Is there any functionality that we are going to lose with the new Teams? Expect some changes on how to access some third-party storage spaces. One benefit is the ability to be active in multiple Teams tenants at the same time. The plan is to have feature parity before the end of this year.
Why should you turn it on today? It’s faster and takes up fewer system resources. But I’m not sure without feature parity you may be disappointed with doing this too soon.
Here are some of the things to expect from Teams 2.0:
- Launch app up to 2X faster
- Join meetings up to 2X faster
- Switch chats/channels up to 1.7X faster
- Consume up to 50% less memory
- Consume up to 70% less disk space
- Streamlined Actions: Less clutter simplifies notifications, search, messages, and channel
- Personalized experiences: Threaded conversations, customizable group chats, and interactive emojis give users more expressive collaboration
- Simplified meetings: Updates to the pre-join experience, gallery view, and screen sharing remove barriers to effective meetings
Check out What’s New in Microsoft Teams at Enterprise Connect 2023
Microsoft Teams Premium
 Tuesday, May 30, 2023 at 12:37PM
Tuesday, May 30, 2023 at 12:37PM  Microsoft Teams Premium is a Teams license that allows organizations with Microsoft 365 subscriptions to enhance their Teams experience with benefits such as more personalized and intelligent meetings and webinars, enhanced protection for meetings, advanced management and reporting capabilities for IT, and advanced Virtual Appointments.
Microsoft Teams Premium is a Teams license that allows organizations with Microsoft 365 subscriptions to enhance their Teams experience with benefits such as more personalized and intelligent meetings and webinars, enhanced protection for meetings, advanced management and reporting capabilities for IT, and advanced Virtual Appointments.
Whether you’re meeting one-on-one, for a webinar, or for a virtual appointment, help make every meeting a perfect fit for your audience. Easily create meetings that meet your specific needs. Use the power of AI to focus on what matters in every meeting. Help keep confidential meetings more protected.
Create personalized meetings in a snap that embody your company brand. Infuse your brand into virtual meetings with custom backgrounds and other options that embody your company brand. Stay focused on the meeting information that matters most with intelligent recap. Apply advanced meeting protection to deter data leaks, enhance encryption, and automate meeting safety options. Turn on advanced features that track business performance, manage queues, and help reduce no-shows. Engage any audience using advanced webinar functionality that automates communications and customizes presenter and attendee experiences.
How NASA Plans to Melt the Moon—and Build on Mars
 Monday, May 29, 2023 at 10:27AM
Monday, May 29, 2023 at 10:27AM Tell me how this article is titled doesn't just jump out at you, make you want to read it. It certainly did for me.
They are using lasers and microwaves in a vacuum to simulate the environment on the moon. If I have peaked your interest just take a minute to read this article.
Microsoft will force all Windows 10 users to upgrade to 'version 22H2' next month
 Monday, May 22, 2023 at 12:19PM
Monday, May 22, 2023 at 12:19PM Windows 10 version 22H2 is the last version of Windows 10, and will be supported by Microsoft until October 2025.
Reminder: End of servicing for Windows 10, version 21H2 Home, Pro, Pro Education, and Pro for Workstations
On June 13, 2023, Home, Pro, Pro Education, and Pro for Workstations editions of Windows 10, version 21H2 will reach end of servicing. The upcoming June 2023 security update, to be released on June 13, 2023, will be the last update available for these versions. After this date, devices running these version will no longer receive monthly security and preview updates containing protections from the latest security threats.To help keep you protected and productive, Windows Update will automatically initiate a feature update for Windows 10 consumer devices and non-managed business devices that are at, or within several months of, reaching end of servicing. This keeps your device supported and receiving monthly updates that are critical to security and ecosystem health. For these devices, you will be able to choose a convenient time for your device to restart and complete the update.As always, we recommend that you update your devices to the latest version of Windows 10, or upgrade eligible devices to Windows 11. For detailed information, see the Windows 10, version 21H2 end of servicing (Home & Pro) lifecycle page. For information about servicing timelines and lifecycle, see Windows 10 release information, Windows 11 release information, Lifecycle FAQ - Windows, and Microsoft Lifecycle Policy search tool.
Work-from-home has its benefits and challenges. Learn more in this whitepaper
 Thursday, May 18, 2023 at 9:50AM
Thursday, May 18, 2023 at 9:50AM  The work-from-home model offers tremendous cost savings and flexibility and is of course, kinder on the environment and provides employees with a better work-life balance. But, it also presents serious IT challenges from the security perspective.
The work-from-home model offers tremendous cost savings and flexibility and is of course, kinder on the environment and provides employees with a better work-life balance. But, it also presents serious IT challenges from the security perspective.
Download our whitepaper, Cybersecurity in a post-pandemic world, to learn more about how you can ensure your business is not a victim of cybercrime even as your employees operate from home.
There are many reasons for installing PAconnect's VOIP phone system for your business.
 Tuesday, May 16, 2023 at 2:45PM
Tuesday, May 16, 2023 at 2:45PM Here are some of the main benefits:
 Cost savings: VOIP phone systems use the internet to make and receive calls, which means you can save on your monthly phone bills and avoid long-distance charges.
Cost savings: VOIP phone systems use the internet to make and receive calls, which means you can save on your monthly phone bills and avoid long-distance charges.- Scalability: VOIP phone systems are easy to expand or reduce as your business needs change. You can add or remove extensions, features, and devices without any hassle or extra cost.
- Mobility: VOIP phone systems allow you to access your phone service from anywhere with an internet connection. You can use your smartphone, tablet, laptop, or desktop as a VOIP device and enjoy the same features and functionality as your office phone.
- Reliability: VOIP phone systems are backed by PAconnect's cloud-based infrastructure, which ensures high-quality voice and data transmission and minimal downtime.
Be sure to call our design team to schedule a demo or to design the perfect system for you!
Call 1-724-838-7526 or contact: Sales@paconnect.com
Interesting Article about Insured companies being more likely to be ransomware victims
 Monday, May 15, 2023 at 1:24PM
Monday, May 15, 2023 at 1:24PM While this headline certainly sounds like you shouldn't be getting the insurance or you will be targeted more it turns out that you really should be getting the insurance and adhering to the the recommendations for increasing your security stance. We like Sophos's MDR Complete product for a more robust product for this purpose for both your workstations and your servers. When you add in some of our other tools that we recommend your protection increases considerably because of the multilevel approach we design.
Training is another key component of protection. Awareness and recognition of potential threats will go a long way to preventing malware issues. There was a time when we were asked why do people create malware but when combined as a ransomeware product the reason is plain and simple, for money! Because of the increase of company's security initiatives, there has been a significant decrease in the payment of ransoms from 85% at the beginning of 2019 to 45% in the first quarter of 2023. Companies are listening and implementing the proper backups and blocks to ransomware that seem to be helping with the need to pay out as often as they did before.
I would suggest taking a look at this article to give you more insight into the protection and insurance levels you should be considering and talk to our security design experts to work with you on developing the proper package for you.
AI Copilot features coming soon to OneNote, Loop, and Whiteboard apps
 Thursday, May 11, 2023 at 2:14PM
Thursday, May 11, 2023 at 2:14PM It is going to be interesting to see how Microsoft's Copilot add in is going to work inside these products. Microsoft has provided a list of Features that we should be looking for. See below:
- Copilot in Whiteboard will make Microsoft Teams meetings and brainstorms more creative and effective. Using natural language, you can ask Copilot to generate ideas, organize ideas into themes, create designs that bring ideas to life and summarize whiteboard content.
- By integrating DALL-E, OpenAI’s image generator, into PowerPoint, users will be able to ask Copilot to create custom images to support their content.
- AI-powered coaching tips and suggestions on clarity, sentiment and tone in Outlook will help users write more effective emails and communicate more confidently.
- Copilot in OneNote will use prompts to draft plans, generate ideas, create lists and organize information to help customers find what they need easily.
- Copilot in Loop helps your team stay in sync by quickly summarizing all the content on your Loop page to keep everyone aligned and able to collaborate effectively.
- Copilot in Viva Learning will use a natural language chat interface to help users create a personalized learning journey including designing upskilling paths, discovering relevant learning resources and scheduling time for assigned trainings.
With Copilot in Microsoft 365, much of that technology is also coming to Office. Unlike Bing AI, however, Copilot for Microsoft 365 is not yet in public preview. Microsoft has been testing it with 20 enterprise customers, and has just announced a paid preview program for 600 enterprise customers to partake in if they wish. There's no word on when Copilot for Microsoft 365 will be available publicly just yet.
OK, Really! Microsoft says people are too tired to work but that AI can help
 Monday, May 8, 2023 at 12:45PM
Monday, May 8, 2023 at 12:45PM Microsoft`s Annual Work Trends Index discussed workers feelings about Artificial Intelligence applications, and how they feel about using them in the workplace. What bothered me the most in the initial paragraphs of the article, Was that two out of thre workers stated that they don't have enough time or energy to Complete their jobs. My question is Whether we are asking too much from our Workers, or is it that we have the work ethic of years past? I don't see the innovation of finding new to increase efficiency even with all the tools we are being handed.
I can see the use case for AI being used to gather non-opinionated data to help with research but we need to be really careful about AI generated opinion pieces because someone had to write the code to help to generate the opinion in the first place. This is very worrisome to me. I think we pay way too much attention to others in social media without thinking fr themselves.
Another interesting result of their poll was that 70% of the workers want to utilize AI in their workplace but on the the other hand, almost half of them were worried that AI might cause them to lose their current jobs. I think this is a needless worry since most managers probably see AI as just another tool for you to make your work more effective. It probably is a possibility if you don't make use of this technology that you might have an issue. But that is that is the case underperforming in any job.
I should think that in any case you should always be on the lookout for any tool at your disposal that will enhance your ability to do your job in a more efficiently with better results.
 AI
AI Microsoft-Window 11-Ads
 Friday, May 5, 2023 at 12:38PM
Friday, May 5, 2023 at 12:38PM Microsoft-Window 11-Ads Microsoft is testing the waters to see how far we let them go with advertising their products inside of Windows 11. It began with the Welcome Screen but with the most recent release of their operating system, we are starting to see it appearing elsewhere.At least it is currently only about their products but how long before they start selling spots to other companies to take advantage of?I would love to from you about your thoughts on this subject.
Microsoft Designer using AI for design help
 Wednesday, May 3, 2023 at 11:21AM
Wednesday, May 3, 2023 at 11:21AM  Microsoft Designer is a new AI-powered design app that helps you create professional-quality designs in less time. With Designer, you can create stunning visuals, social media posts, invitations, and more using cutting-edge generative AI technology.
Microsoft Designer is a new AI-powered design app that helps you create professional-quality designs in less time. With Designer, you can create stunning visuals, social media posts, invitations, and more using cutting-edge generative AI technology.
Here are some of the things you can do with Microsoft Designer:
- Create stunning visuals: Designer has a library of over 1 million high-quality images that you can use to create your designs. You can also use Designer to generate your own images by simply describing what you want.
- Create social media posts: Designer has a variety of templates that you can use to create social media posts. You can also use Designer to create custom designs for your social media channels.
- Create invitations: Designer has a variety of templates that you can use to create invitations. You can also use Designer to create custom designs for your invitations.
- Create more with less: Designer uses AI to help you create designs faster and easier. With Designer, you can focus on your creativity and let the AI take care of the rest.
Microsoft Designer is a powerful tool that can help you create professional-quality designs in less time. If you're looking for a way to improve your design skills, Designer is a great option.
Here are some of the benefits of using Microsoft Designer:
- Create professional-quality designs: Designer uses AI to help you create designs that are both visually appealing and effective.
- Save time: Designer can help you save time by automating many of the tasks involved in design, such as finding images and creating layouts.
- Be more creative: Designer can help you be more creative by giving you access to a wide range of tools and resources.
- Collaborate with others: Designer makes it easy to collaborate with others on design projects. You can share designs with others and get feedback in real time.
If you're looking for a powerful design tool that can help you create professional-quality designs in less time, Microsoft Designer is a great option.


